您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
今天小編給大家分享一下python的pip-audit安全漏洞掃描工具怎么用的相關知識點,內容詳細,邏輯清晰,相信大部分人都還太了解這方面的知識,所以分享這篇文章給大家參考一下,希望大家閱讀完這篇文章后有所收獲,下面我們一起來了解一下吧。
pip-audit是一款功能強大的安全漏洞掃描工具,該工具主要針對Python環境,可以幫助廣大研究人員掃描和測試Python包中的已知安全漏洞。pip-audit使用了PythonPackagingAdvisory數據庫PyPIJSONAPI作為漏洞報告源。
1、支持對本地環境和依賴組件(requirements風格文件)進行安全審計;
2、支持多種漏洞服務(PyPI、OSV);
3、支持以CycloneDX XML或JSON格式發送SBOM;
4、提供人類和機器均可讀的輸出格式(columnar、JSON);
5、無縫接入 / 重用本地pip緩存;
pip-audit基于Python開發,且要求本地環境為Python 3.7或更新版本。安裝并配置好Python環境之后,就可以使用下列命令并通過pip來安裝pip-audit了:
python -m pip install pip-audit
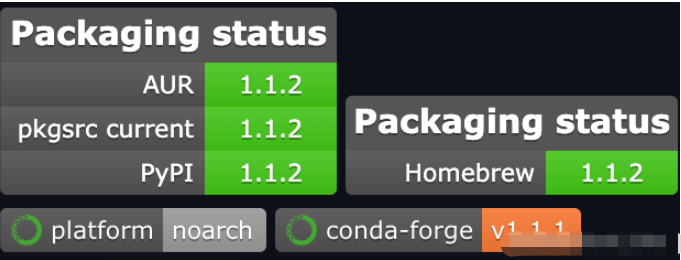
pip-audit的正常運行需要使用到多個第三方包,具體組件包名稱和版本如下圖所示:
除此之外,我們還可以通過conda來安裝pip-audit:
conda install -c conda-forge pip-audit
我們可以直接將pip-audit以獨立程序運行,或通過“python -m”運行:
pip-audit --help python -m pip_audit --help
usage: pip-audit [-h] [-V] [-l] [-r REQUIREMENTS] [-f FORMAT] [-s SERVICE]
[-d] [-S] [--desc [{on,off,auto}]] [--cache-dir CACHE_DIR]
[--progress-spinner {on,off}] [--timeout TIMEOUT]
[--path PATHS] [-v] [--fix] [--require-hashes]
audit the Python environment for dependencies with known vulnerabilities
optional arguments:
-h, --help show this help message and exit
-V, --version show program's version number and exit
-l, --local show only results for dependencies in the local
environment (default: False)
-r REQUIREMENTS, --requirement REQUIREMENTS
audit the given requirements file; this option can be
used multiple times (default: None)
-f FORMAT, --format FORMAT
the format to emit audit results in (choices: columns,
json, cyclonedx-json, cyclonedx-xml) (default:
columns)
-s SERVICE, --vulnerability-service SERVICE
the vulnerability service to audit dependencies
against (choices: osv, pypi) (default: pypi)
-d, --dry-run without `--fix`: collect all dependencies but do not
perform the auditing step; with `--fix`: perform the
auditing step but do not perform any fixes (default:
False)
-S, --strict fail the entire audit if dependency collection fails
on any dependency (default: False)
--desc [{on,off,auto}]
include a description for each vulnerability; `auto`
defaults to `on` for the `json` format. This flag has
no effect on the `cyclonedx-json` or `cyclonedx-xml`
formats. (default: auto)
--cache-dir CACHE_DIR
the directory to use as an HTTP cache for PyPI; uses
the `pip` HTTP cache by default (default: None)
--progress-spinner {on,off}
display a progress spinner (default: on)
--timeout TIMEOUT set the socket timeout (default: 15)
--path PATHS restrict to the specified installation path for
auditing packages; this option can be used multiple
times (default: [])
-v, --verbose give more output; this setting overrides the
`PIP_AUDIT_LOGLEVEL` variable and is equivalent to
setting it to `debug` (default: False)
--fix automatically upgrade dependencies with known
vulnerabilities (default: False)
--require-hashes require a hash to check each requirement against, for
repeatable audits; this option is implied when any
package in a requirements file has a `--hash` option.
(default: False)任務完成后, pip-audit將會退出運行,并返回一個代碼以顯示其狀態,其中:
0:未檢測到已知漏洞;
1:檢測到了一個或多個已知漏洞;
審計當前Python環境中的依賴:
$ pip-audit No known vulnerabilities found
審計給定requirements文件的依賴:
$ pip-audit -r ./requirements.txt No known vulnerabilities found
審計一個requirements文件,并排除系統包:
$ pip-audit -r ./requirements.txt -l No known vulnerabilities found
審計依賴中發現的安全漏洞:
$ pip-audit Found 2 known vulnerabilities in 1 package Name Version ID Fix Versions ---- ------- -------------- ------------ Flask 0.5 PYSEC-2019-179 1.0 Flask 0.5 PYSEC-2018-66 0.12.3
審計依賴(包含描述):
$ pip-audit --desc Found 2 known vulnerabilities in 1 package Name Version ID Fix Versions Description ---- ------- -------------- ------------ -------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- Flask 0.5 PYSEC-2019-179 1.0 The Pallets Project Flask before 1.0 is affected by: unexpected memory usage. The impact is: denial of service. The attack vector is: crafted encoded JSON data. The fixed version is: 1\. NOTE: this may overlap CVE-2018-1000656. Flask 0.5 PYSEC-2018-66 0.12.3 The Pallets Project flask version Before 0.12.3 contains a CWE-20: Improper Input Validation vulnerability in flask that can result in Large amount of memory usage possibly leading to denial of service. This attack appear to be exploitable via Attacker provides JSON data in incorrect encoding. This vulnerability appears to have been fixed in 0.12.3\. NOTE: this may overlap CVE-2019-1010083.
審計JSON格式依賴:
$ pip-audit -f json | jq
Found 2 known vulnerabilities in 1 package
[
{
"name": "flask",
"version": "0.5",
"vulns": [
{
"id": "PYSEC-2019-179",
"fix_versions": [
"1.0"
],
"description": "The Pallets Project Flask before 1.0 is affected by: unexpected memory usage. The impact is: denial of service. The attack vector is: crafted encoded JSON data. The fixed version is: 1\. NOTE: this may overlap CVE-2018-1000656."
},
{
"id": "PYSEC-2018-66",
"fix_versions": [
"0.12.3"
],
"description": "The Pallets Project flask version Before 0.12.3 contains a CWE-20: Improper Input Validation vulnerability in flask that can result in Large amount of memory usage possibly leading to denial of service. This attack appear to be exploitable via Attacker provides JSON data in incorrect encoding. This vulnerability appears to have been fixed in 0.12.3\. NOTE: this may overlap CVE-2019-1010083."
}
]
},
{
"name": "jinja2",
"version": "3.0.2",
"vulns": []
},
{
"name": "pip",
"version": "21.3.1",
"vulns": []
},
{
"name": "setuptools",
"version": "57.4.0",
"vulns": []
},
{
"name": "werkzeug",
"version": "2.0.2",
"vulns": []
},
{
"name": "markupsafe",
"version": "2.0.1",
"vulns": []
}
]審計并嘗試自動審計存在漏洞的依賴:
$ pip-audit --fix Found 2 known vulnerabilities in 1 package and fixed 2 vulnerabilities in 1 package Name Version ID Fix Versions Applied Fix ----- ------- -------------- ------------ ---------------------------------------- flask 0.5 PYSEC-2019-179 1.0 Successfully upgraded flask (0.5 => 1.0) flask 0.5 PYSEC-2018-66 0.12.3 Successfully upgraded flask (0.5 => 1.0)
本項目的開發與發布遵循 Apache 2.0開源許可證協議。
以上就是“python的pip-audit安全漏洞掃描工具怎么用”這篇文章的所有內容,感謝各位的閱讀!相信大家閱讀完這篇文章都有很大的收獲,小編每天都會為大家更新不同的知識,如果還想學習更多的知識,請關注億速云行業資訊頻道。
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。