您好,登錄后才能下訂單哦!
您好,登錄后才能下訂單哦!
下文給大家帶來怎么樣分配公網證書基于負載均衡-Keepalived-Haproxy,希望能夠給大家在實際運用中帶來一定的幫助,負載均衡涉及的東西比較多,理論也不多,網上有很多書籍,今天我們就用億速云在行業內累計的經驗來做一個解答。
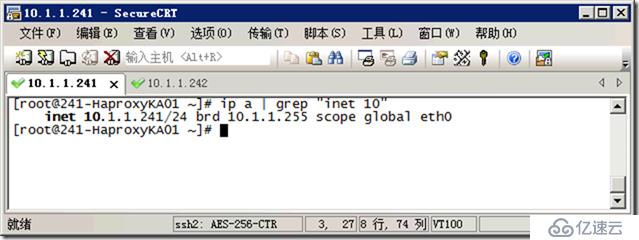
241-HaproxyKA01
242-HaproxyKA02
同樣配置。
// 0. 刪除文件

//刪除舊證書:
ll certificates/
rm -f certificates/*.* //刪除所有
ll certificates/
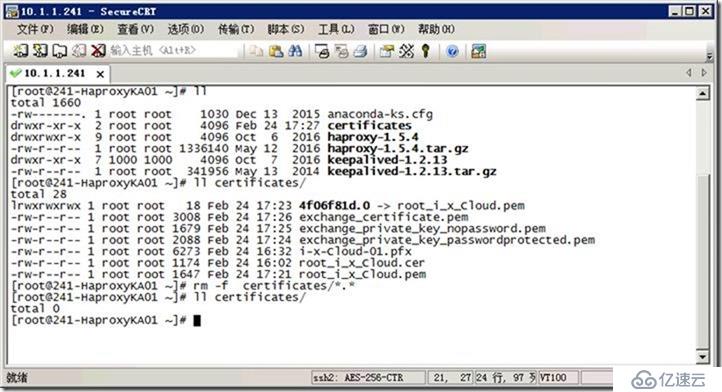
//刪除證書
ll /etc/ssl/certs/
rm -f /etc/ssl/certs/exchange_certificate_and_key_nopassword.pem //刪除此文件
ll /etc/ssl/certs/
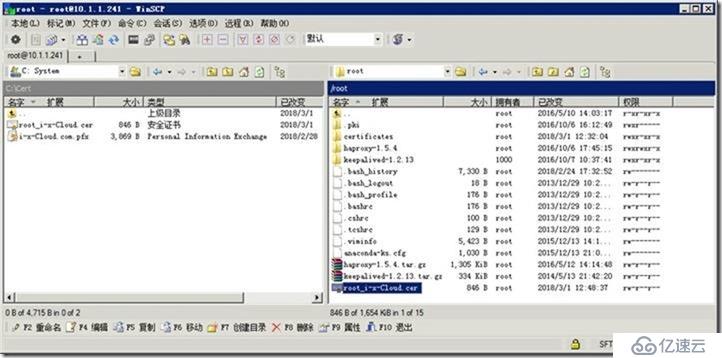
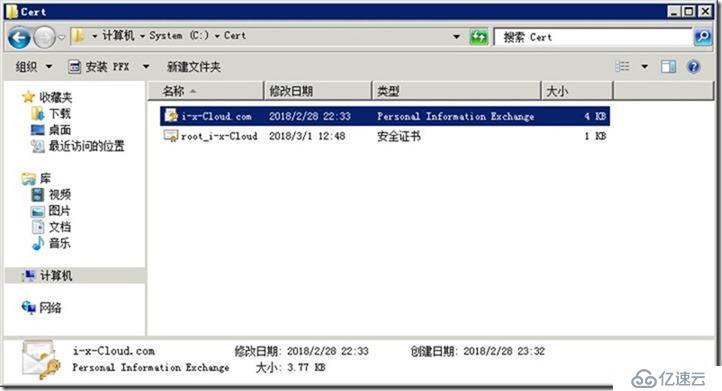
// 1.下載 CA 證書(根證書)
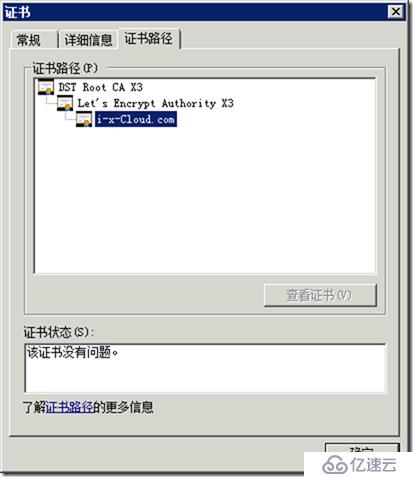
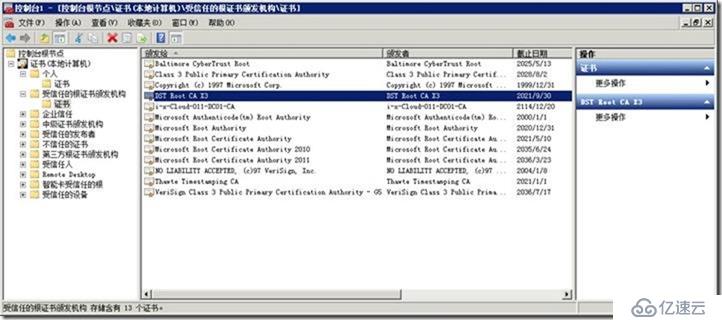
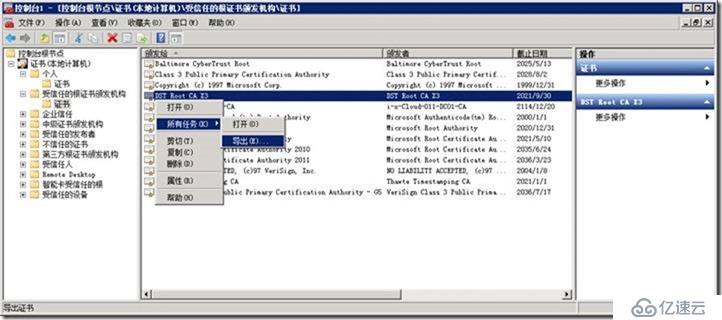
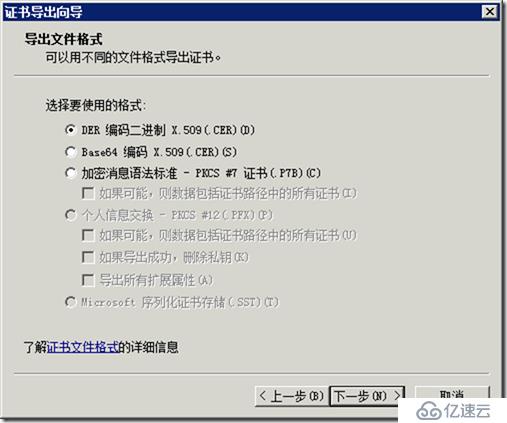
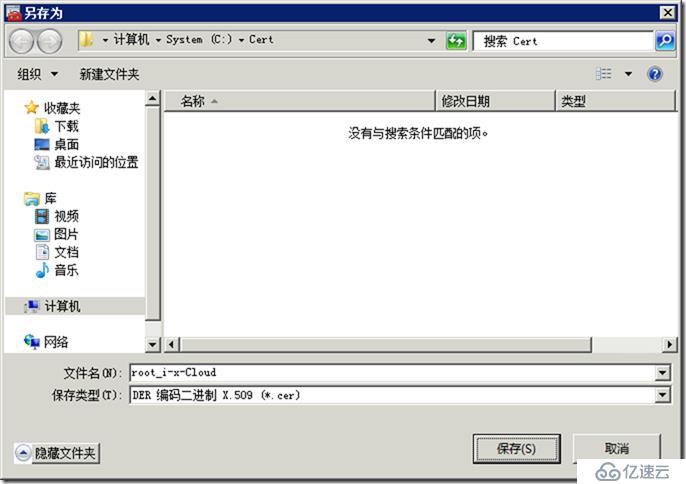
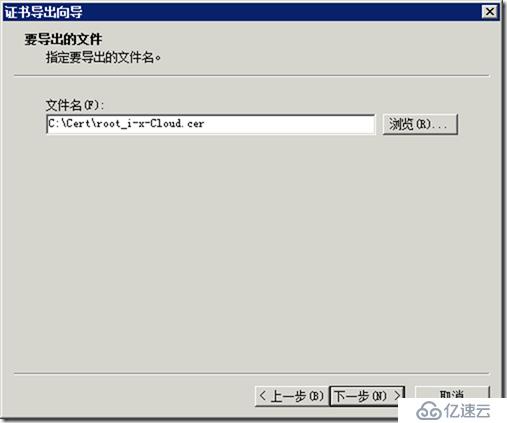
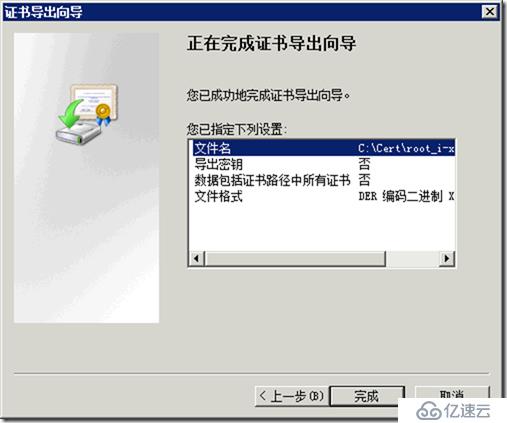
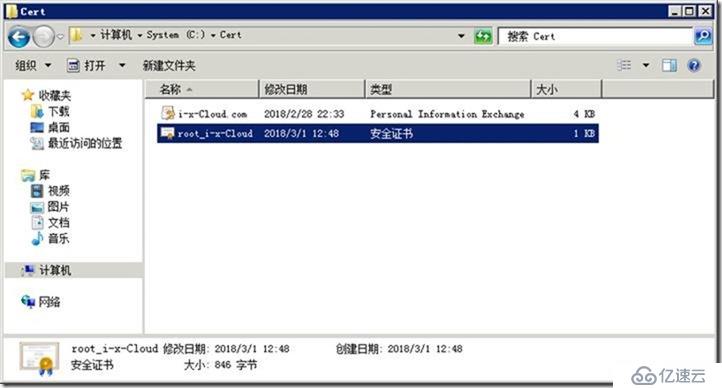
root_i-x-Cloud.cer
上傳到 /root/
ls *.cer -l
mv *.cer certificates/
cd certificates
ll
[root@241-HaproxyKA01 ~]# ll
total 1660
-rw-------. 1 root root 1030 Dec 13 2015 anaconda-ks.cfg
drwxr-xr-x 2 root root 6 Feb 24 17:18 certificates
drwxrwxr-x 9 root root 4096 Oct 6 2016 haproxy-1.5.4
-rw-r--r-- 1 root root 1336140 May 12 2016 haproxy-1.5.4.tar.gz
drwxr-xr-x 7 1000 1000 4096 Oct 7 2016 keepalived-1.2.13
-rw-r--r-- 1 root root 341956 May 13 2014 keepalived-1.2.13.tar.gz
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i_x_Cloud.cer
[root@241-HaproxyKA01 ~]# mv *.cer certificates/
[root@241-HaproxyKA01 ~]# cd certificates/
[root@241-HaproxyKA01 certificates]# ll
total 4
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i_x_Cloud.cer

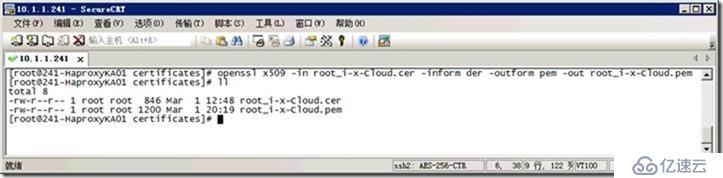
// 2. 將cer轉為pem (根證書)
openssl x509 -in root_i-x-Cloud.cer -inform der -outform pem -out root_i-x-Cloud.pem
ll
[root@241-HaproxyKA01 certificates]# openssl x509 -in root_i-x-Cloud.cer -inform der -outform pem -out root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# ll
total 8
-rw-r--r-- 1 root root 1174 Feb 24 16:02 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1647 Feb 24 17:21 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
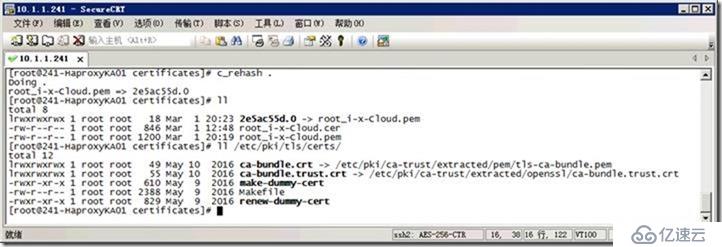
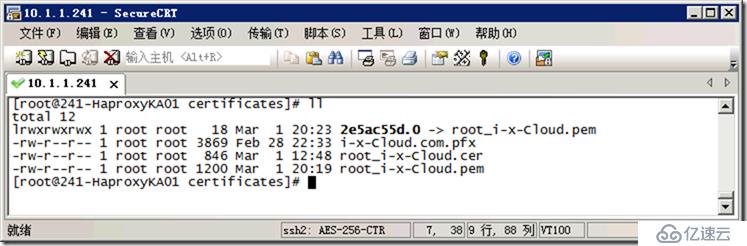
// 3. 重新生成hash
[root@241-HaproxyKA01 certificates]# c_rehash .
Doing .
root_i-x-Cloud.pem => 2e5ac55d.0
[root@241-HaproxyKA01 certificates]# ll
total 8
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# ll /etc/pki/tls/certs/
total 12
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]#
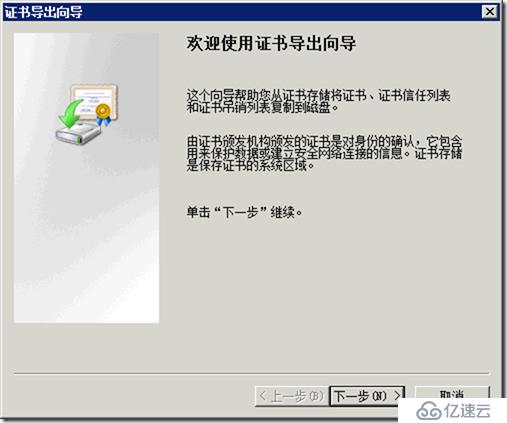
// 4. 導出證書(設置密碼:Aa123456)//密碼不能為1.
i-x-Cloud.com.pfx
上傳證書:/root/certificates/
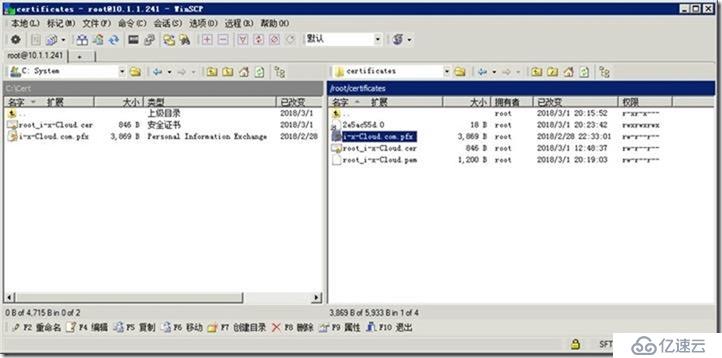
[root@241-HaproxyKA01 certificates]# ll
total 12
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3869 Feb 28 22:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
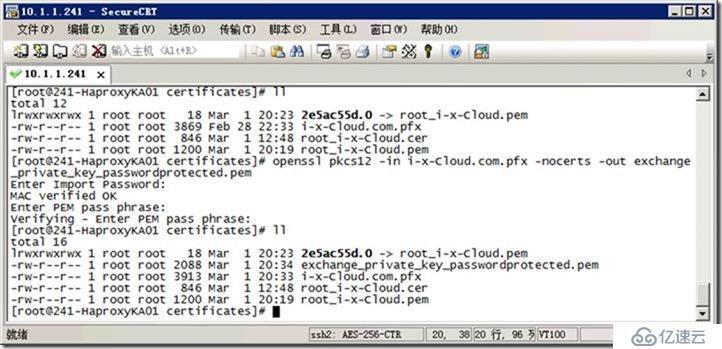
// 5. 將pfx轉為pem
openssl pkcs12 -in i-x-Cloud.com.pfx -nocerts -out exchange_private_key_passwordprotected.pem
Aa123456
[root@241-HaproxyKA01 certificates]# ll
total 12
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3869 Feb 28 22:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]# openssl pkcs12 -in i-x-Cloud.com.pfx -nocerts -out exchange_private_key_passwordprotected.pem
Enter Import Password:
MAC verified OK
Enter PEM pass phrase:
Verifying - Enter PEM pass phrase:
[root@241-HaproxyKA01 certificates]# ll
total 16
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
// 6. 移出密碼保護
openssl rsa -in exchange_private_key_passwordprotected.pem -out exchange_private_key_nopassword.pem
[root@241-HaproxyKA01 certificates]# openssl rsa -in exchange_private_key_passwordprotected.pem -out exchange_private_key_nopassword.pem
Enter pass phrase for exchange_private_key_passwordprotected.pem:
writing RSA key
[root@241-HaproxyKA01 certificates]# ll
total 20
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
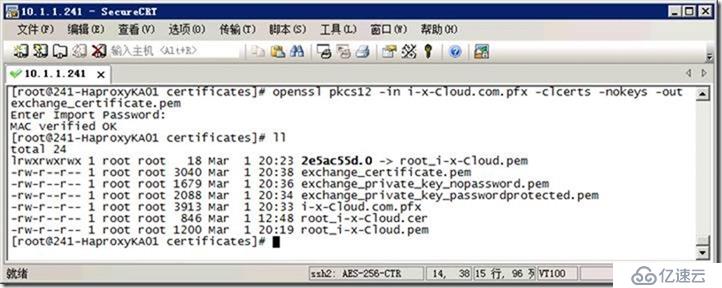
// 7. 解壓這個pfx文件,我們需要提供憑證。
openssl pkcs12 -in i-x-Cloud.com.pfx -clcerts -nokeys -out exchange_certificate.pem
ll
[root@241-HaproxyKA01 certificates]# openssl pkcs12 -in i-x-Cloud.com.pfx -clcerts -nokeys -out exchange_certificate.pem
Enter Import Password:
MAC verified OK
[root@241-HaproxyKA01 certificates]# ll
total 24
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
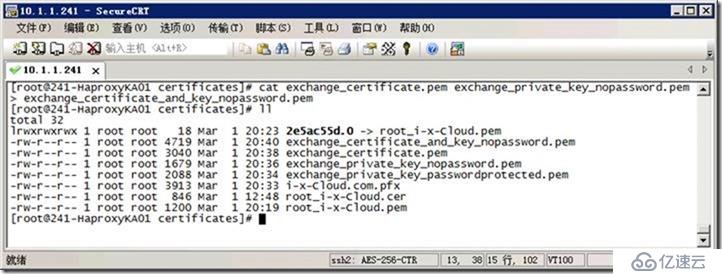
// 8. 通過將exchange_certificate.pem和exchange_private_key_nopassword.pem產生exchange_certificate_and_key_nopassword.pem。
cat exchange_certificate.pem exchange_private_key_nopassword.pem > exchange_certificate_and_key_nopassword.pem
ll
[root@241-HaproxyKA01 certificates]# cat exchange_certificate.pem exchange_private_key_nopassword.pem > exchange_certificate_and_key_nopassword.pem
[root@241-HaproxyKA01 certificates]# ll
total 32
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 4719 Mar 1 20:40 exchange_certificate_and_key_nopassword.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
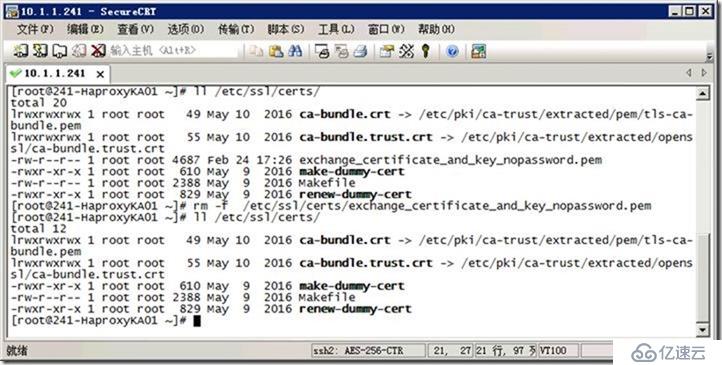
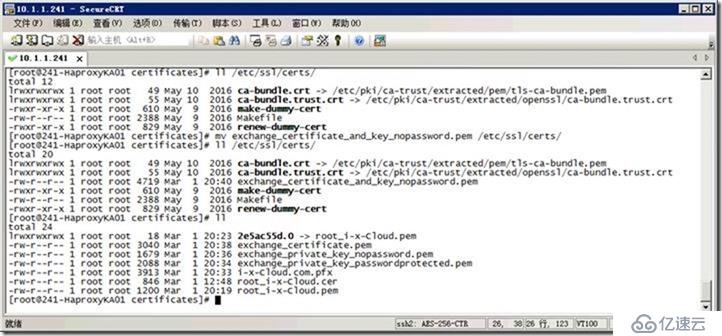
// 9. 復制到文件夾中
ll /etc/ssl/certs/
rm -f /etc/ssl/certs/exchange_certificate_and_key_nopassword.pem
mv exchange_certificate_and_key_nopassword.pem /etc/ssl/certs/
ll /etc/ssl/certs/
ll
[root@241-HaproxyKA01 certificates]# ll /etc/ssl/certs/
total 12
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]# mv exchange_certificate_and_key_nopassword.pem /etc/ssl/certs/
[root@241-HaproxyKA01 certificates]# ll /etc/ssl/certs/
total 20
lrwxrwxrwx 1 root root 49 May 10 2016 ca-bundle.crt -> /etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem
lrwxrwxrwx 1 root root 55 May 10 2016 ca-bundle.trust.crt -> /etc/pki/ca-trust/extracted/openssl/ca-bundle.trust.crt
-rw-r--r-- 1 root root 4719 Mar 1 20:40 exchange_certificate_and_key_nopassword.pem
-rwxr-xr-x 1 root root 610 May 9 2016 make-dummy-cert
-rw-r--r-- 1 root root 2388 May 9 2016 Makefile
-rwxr-xr-x 1 root root 829 May 9 2016 renew-dummy-cert
[root@241-HaproxyKA01 certificates]# ll
total 24
lrwxrwxrwx 1 root root 18 Mar 1 20:23 2e5ac55d.0 -> root_i-x-Cloud.pem
-rw-r--r-- 1 root root 3040 Mar 1 20:38 exchange_certificate.pem
-rw-r--r-- 1 root root 1679 Mar 1 20:36 exchange_private_key_nopassword.pem
-rw-r--r-- 1 root root 2088 Mar 1 20:34 exchange_private_key_passwordprotected.pem
-rw-r--r-- 1 root root 3913 Mar 1 20:33 i-x-Cloud.com.pfx
-rw-r--r-- 1 root root 846 Mar 1 12:48 root_i-x-Cloud.cer
-rw-r--r-- 1 root root 1200 Mar 1 20:19 root_i-x-Cloud.pem
[root@241-HaproxyKA01 certificates]#
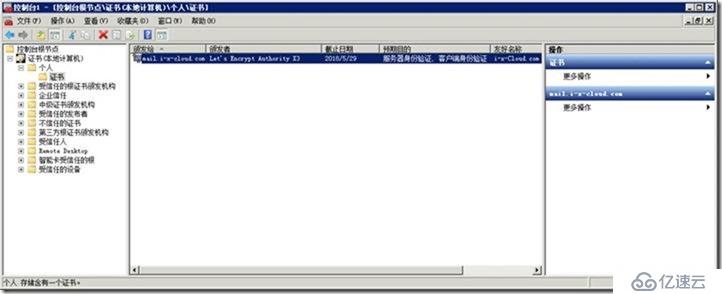
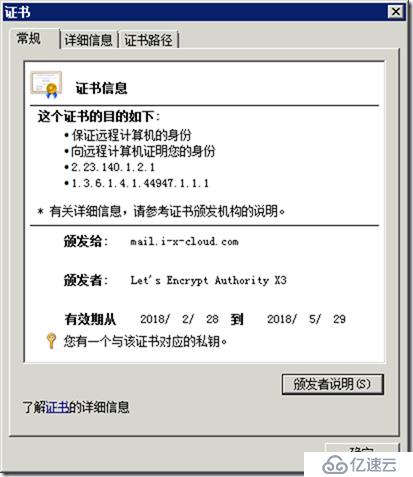
// 10. 測試
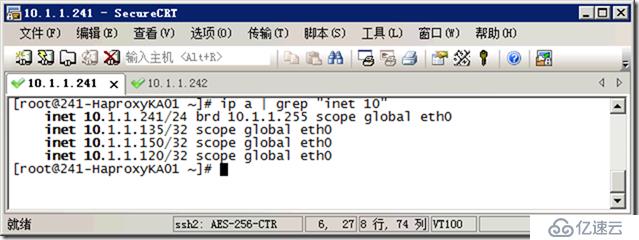
[root@241-HaproxyKA01 ~]# ip a | grep "inet 10"
inet 10.1.1.241/24 brd 10.1.1.255 scope global eth0
inet 10.1.1.135/32 scope global eth0
inet 10.1.1.150/32 scope global eth0
inet 10.1.1.120/32 scope global eth0
[root@241-HaproxyKA01 ~]#
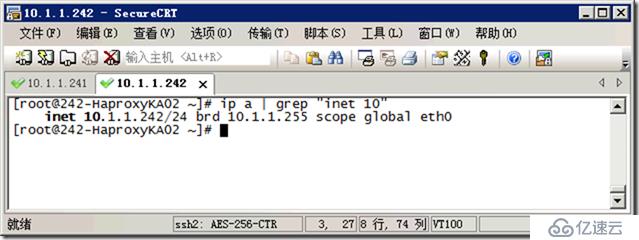
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
[root@242-HaproxyKA02 ~]#
[root@241-HaproxyKA01 ~]# ip a | grep "inet 10"
inet 10.1.1.241/24 brd 10.1.1.255 scope global eth0
[root@241-HaproxyKA01 ~]#
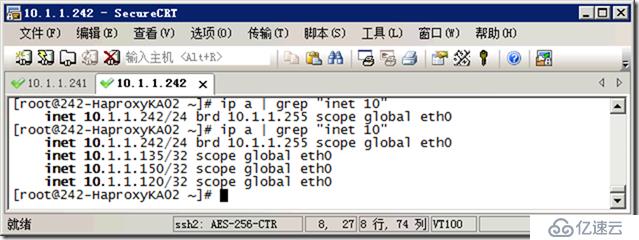
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
[root@242-HaproxyKA02 ~]# ip a | grep "inet 10"
inet 10.1.1.242/24 brd 10.1.1.255 scope global eth0
inet 10.1.1.135/32 scope global eth0
inet 10.1.1.150/32 scope global eth0
inet 10.1.1.120/32 scope global eth0
[root@242-HaproxyKA02 ~]#
看了以上關于怎么樣分配公網證書基于負載均衡-Keepalived-Haproxy,如果大家還有什么地方需要了解的可以在億速云行業資訊里查找自己感興趣的或者找我們的專業技術工程師解答的,億速云技術工程師在行業內擁有十幾年的經驗了。億速云官網鏈接www.5655pk.com
免責聲明:本站發布的內容(圖片、視頻和文字)以原創、轉載和分享為主,文章觀點不代表本網站立場,如果涉及侵權請聯系站長郵箱:is@yisu.com進行舉報,并提供相關證據,一經查實,將立刻刪除涉嫌侵權內容。